A PowerShell script to list all installed Microsoft Windows Updates

PowerShell Version 2 or Greater required.
Why use this script?
The PowerShell cmdlet ‘get-hotfix’ sometimes does not draw-out ‘installedon’ information. win32-Quickfixengineering class does not have that information either. <SIGH>
What does this script offer?
The above void can be filled by using the good old ‘wmic qfe list’ command. But, the output of the legacy command is mere text and cannot be easily interrogated like objects in PowerShell.
The attached script converts the output string of ‘wmic qfe list’ command into versatile PowerShell objects, which can be used within other scripts.
Note: Do not forget to include the attached powershell script.
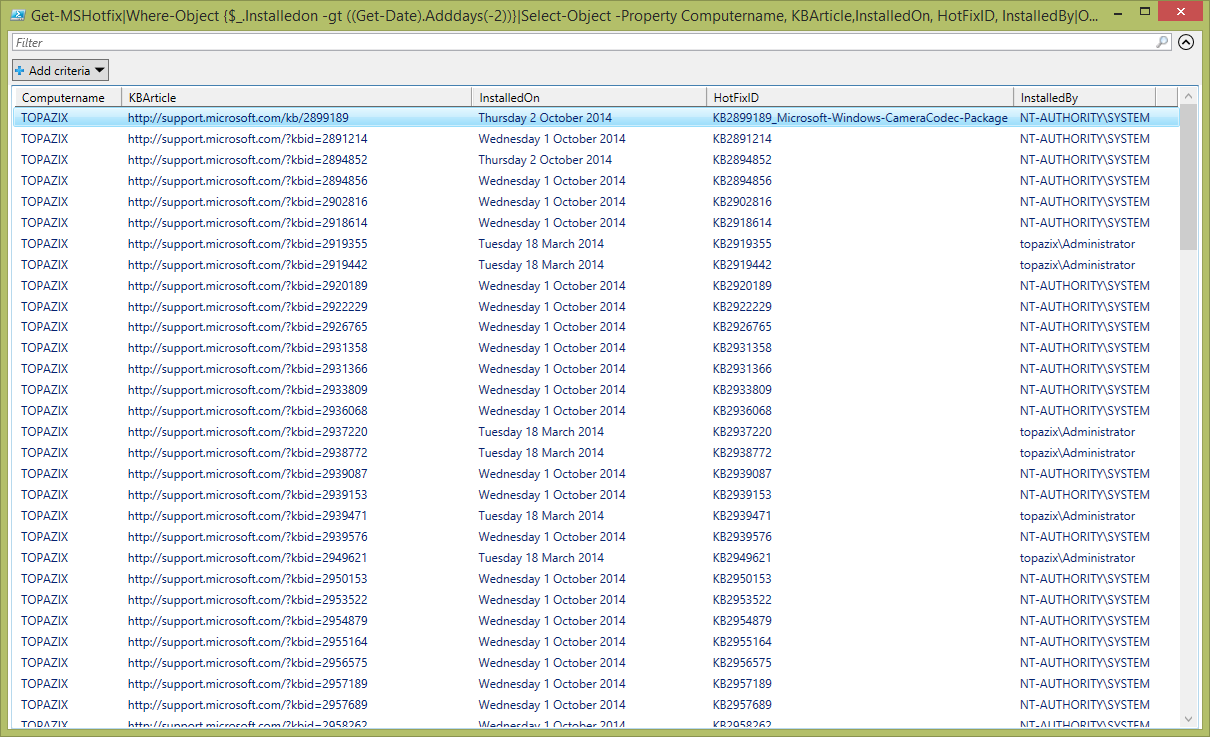
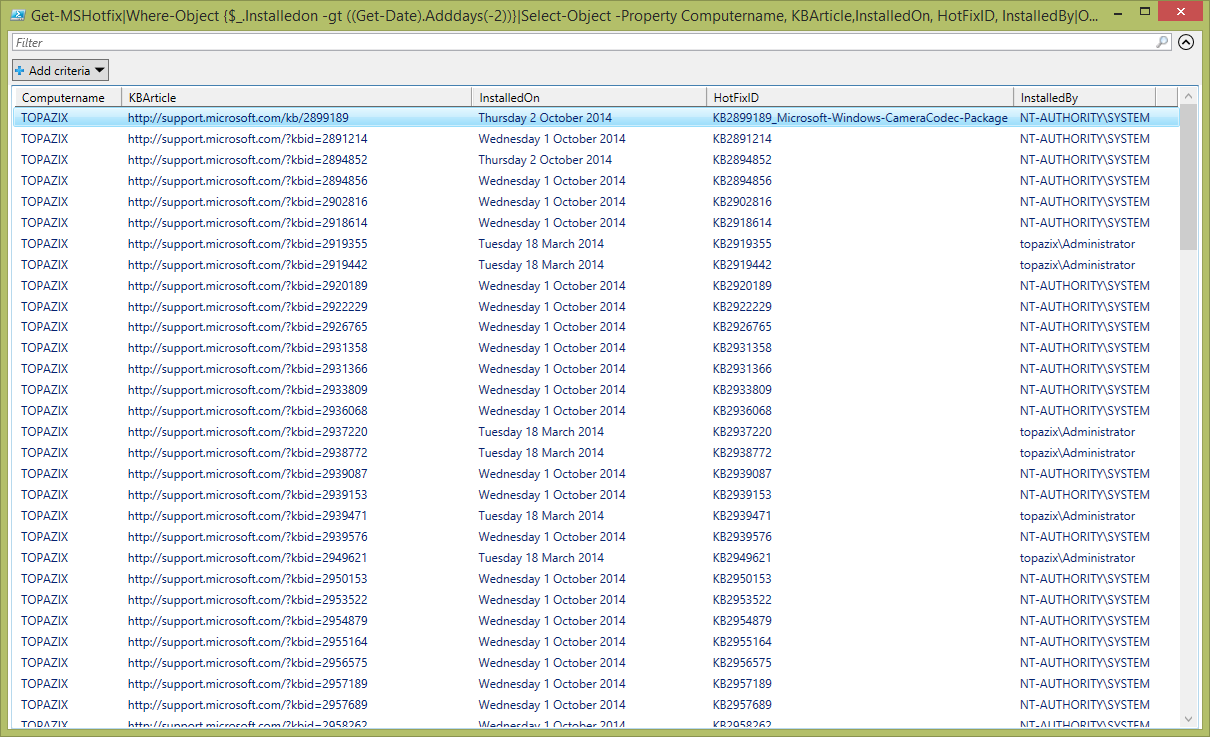
The below POSH oneliner lists all updates installed in the last 2 days and tabulates properties: Computername, KBArticle,InstalledOn, HotFixID and InstalledBy.
Get-MSHotfix|Where-Object {$_.Installedon -gt ((Get-Date).Adddays(-2))}|Select-Object -Property Computername, KBArticle,InstalledOn, HotFixID, InstalledBy|Format-Table
The below powershell command-line will output details about the hotfix with ID ‘2953522’.
Get-MSHotfix|Where-Object {$_.HotfixID -match "KB2953522"}
The below POSH gem opens the Knowledge Base webpage for the hotfix with ID ‘2953522’.
Get-MSHotfix|Where-Object {$_.HotfixID -match "KB2953522"}|ForEach-Object {[System.Diagnostics.Process]::Start($_.KBArticle)}
Script Content:
Function Get-MSHotfix
{
$outputs = Invoke-Expression "wmic qfe list"
$outputs = $outputs[1..($outputs.length)]
foreach ($output in $Outputs) {
if ($output) {
$output = $output -replace 'Security Update','Security-Update'
$output = $output -replace 'NT AUTHORITY','NT-AUTHORITY'
$output = $output -replace '\s+',' '
$parts = $output -split ' '
if ($parts[5] -like "*/*/*") {
$Dateis = [datetime]::ParseExact($parts[5], '%M/%d/yyyy',[Globalization.cultureinfo]::GetCultureInfo("en-US").DateTimeFormat)
} else {
$Dateis = get-date([DateTime][Convert]::ToInt64("$parts[5]", 16)) -Format '%M/%d/yyyy'
}
New-Object -Type PSObject -Property @{
KBArticle = [string]$parts[0]
Computername = [string]$parts[1]
Description = [string]$parts[2]
FixComments = [string]$parts[6]
HotFixID = [string]$parts[3]
InstalledOn = Get-Date($Dateis)-format "dddd d MMMM yyyy"
InstalledBy = [string]$parts[4]
InstallDate = [string]$parts[7]
Name = [string]$parts[8]
ServicePackInEffect = [string]$parts[9]
Status = [string]$parts[10]
}
}
}
}
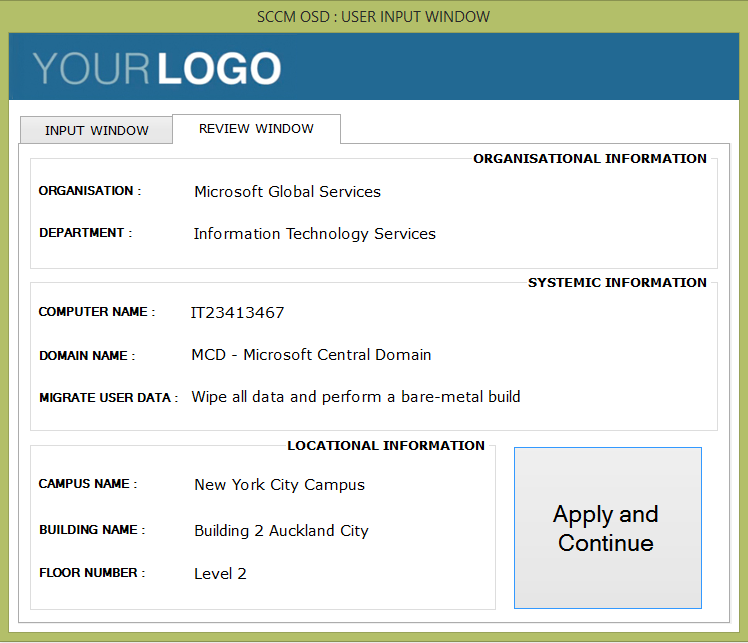
The following script can be used as a template to run this function against multiple machines. For this to work you have to enable PSRemoting on all the machines.
$scriptDirectory = Split-Path -Parent $MyInvocation.MyCommand.Definition
."$scriptDirectory\Get-MSHotfix.ps1"
$allUpdates = ''
$array = @("host1", "host2", "host3")
for ($i=0; $i -lt $array.length; $i++) {
$Updates = Invoke-Command -ComputerName $array[$i] ${function:Get-MSHotfix}|ft -HideTableHeaders
$allUpdates += $Updates
}
$allUpdates
Further notes:
Output of the ‘get-wmiobject -class win32_quickfixengineering‘ command: InstalledOn property NOT available for all updates.
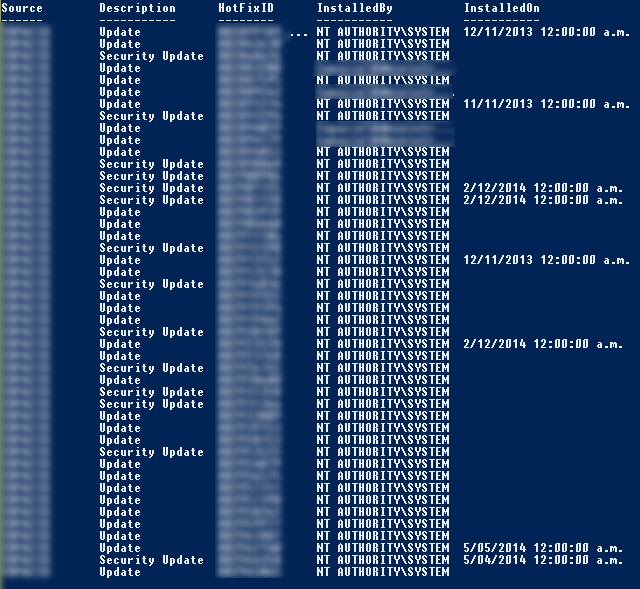
Output of the ‘wmic qfe list’ command: Installedon property available for all updates.

Output of Get-MSHotfix:


Super like. Thanks for the share.